On Friday, May 12, a ransomware variant titled “WannaCry” infiltrated several UK-based National Health Service locations. Since then, it has spread across 200 countries and infected more than 200,000 endpoints.
Three WannaCry Facts You Should Know
Fact 1
WannaCry is a ransomware variant that leverages a known Microsoft SMB vulnerability (EternalBlue).
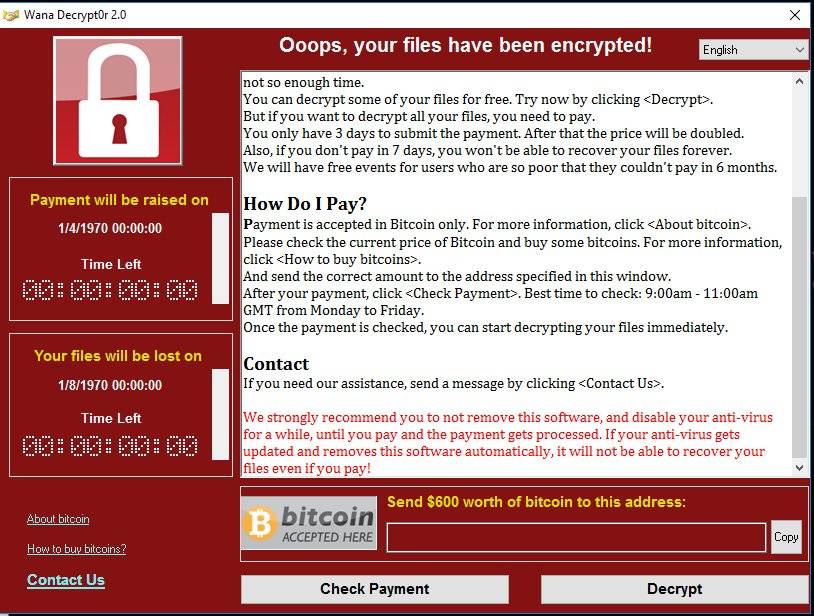
Targeting unpatched Windows operating systems (Windows XP, 8, Vista, 7, 2012, 10, and Server 2003). Infected users experience file encryption in exchange for a $300 bitcoin ransom. The malware has been documented propagating laterally, rapidly infecting affiliated endpoints.
Fact 2
Microsoft has since released a patch to fix legacy operating systems (Windows XP and onward).
While a patch to remove the underlying vulnerability (Windows Vista and onward) had been issued on March 14, delays in applying security updates, and lack of support by Microsoft for legacy Windows versions have left users vulnerable.
Fact 3
A short-term “kill-switch” was identified that prevented the infection of additional systems.
Since then, new variants of the malware, which lack the kill-switch, have been reported. As of May 15, 2017, the threat is still prevalent and at large.
WannaCry Details and Misconceptions
Important information is getting lost amongst the online clutter – take the time to eliminate all WannaCry misconceptions.
- The most common WannaCry variant uses IPC$ shares and SMB resources to propagate.
- WannaCry leverages the exploit EternalBlue – the vulnerability drops an executable onto the targeted system and conducts a beacon check for the kill-switch domain. If it doesn’t receive a response, then the malware executes the ransomware routines.
- WannaCry installs the DOUBLEPULSAR backdoor. It corrupts shadow volumes to make recovery harder. (Source: Malwarebytes)
- On the LAN, it scans for all enumerated addresses within its LAN with an open port 445 & 139 (i.e. the SMB port).
- On the internet, it scans for random IP addresses to see if it has an open port 445. If it finds one with an open port, it scans all devices in the same /24 IP range (i.e. IP addresses that share the first three octets) as the found address.
- WannaCry kills SQL Server, Exchange, MySQL and installs TOR on the endpoint.
- When the ransom demand-time elapses, the malware writes up to 1GB of free space on host-disk and then deletes the file.
- A variant of WannaCry has been previously documented before this instance.
A Cost-benefit Analysis Can Help When It Comes To Ransomware
We live in the real world and often we work for companies looking to maximize their profits. It is practical for them to perform a risk-based cost benefit analysis to determine whether to pay or not. To pay or not should be a business decision based on which option is most cost effective. Consider these variables:
![]()
Question 1
What will happen if you lose your data?
Is the data or system critical in nature? What is the potential impact to the information system, the business process, or the organization? Are there adequate backups and a recovery process to minimize operational interruptions?
![]()
Question 2
What is the relative cost associated with paying?
Most ransom demands are meant to be reasonable to incite you to pay.
![]()
Question 3
What is the probability that your data will be decrypted?
An “unethical” extortionist could receive payment and choose not to decrypt your data.
![]()
Question 4
What are the chances this will happen again?
An attacker could leave malware on your systems in the form of a backdoor, which they could use to compromise you for additional ransom. An attacker could also spread the knowledge that you are willing to pay, inciting other cybercriminals to attack you.
A Good Strategy Is the Key
WannaCry is a good reminder that security threats are often unknown and unpredictable. The only way to maintain effective defense is through a comprehensive and flexible security program.
Prevent
Defense in depth is the best approach to protect against unknown and unpredictable attacks. Effective anti-malware, diligent patching and vulnerability management, and strong human-centric security are essential.
Detect
There are two types of companies – those who have been breached and know it, and those who have been breached and don’t know it. Ensure that monitoring, logging, and event detection tools are in place and appropriate to your organizational needs.
Analyze
Raw data without interpretation cannot improve security, and is a waste of time, money, and effort. Establish a tiered operational process that not only enriches data but provides visibility into your threat landscape.
Respond
Organizations can’t rely on an ad-hoc response anymore – don’t wait until a state of panic. Formalize your response processes in a detailed incident runbook in order to reduce incident remediation time and effort.
Not sure where you should start? We can help…
Call us at 585.292.5070 to speak directly with one of our information security experts. If you don’t want to call, you can always contact us via email.

