
What is an IT Security Snapshot?
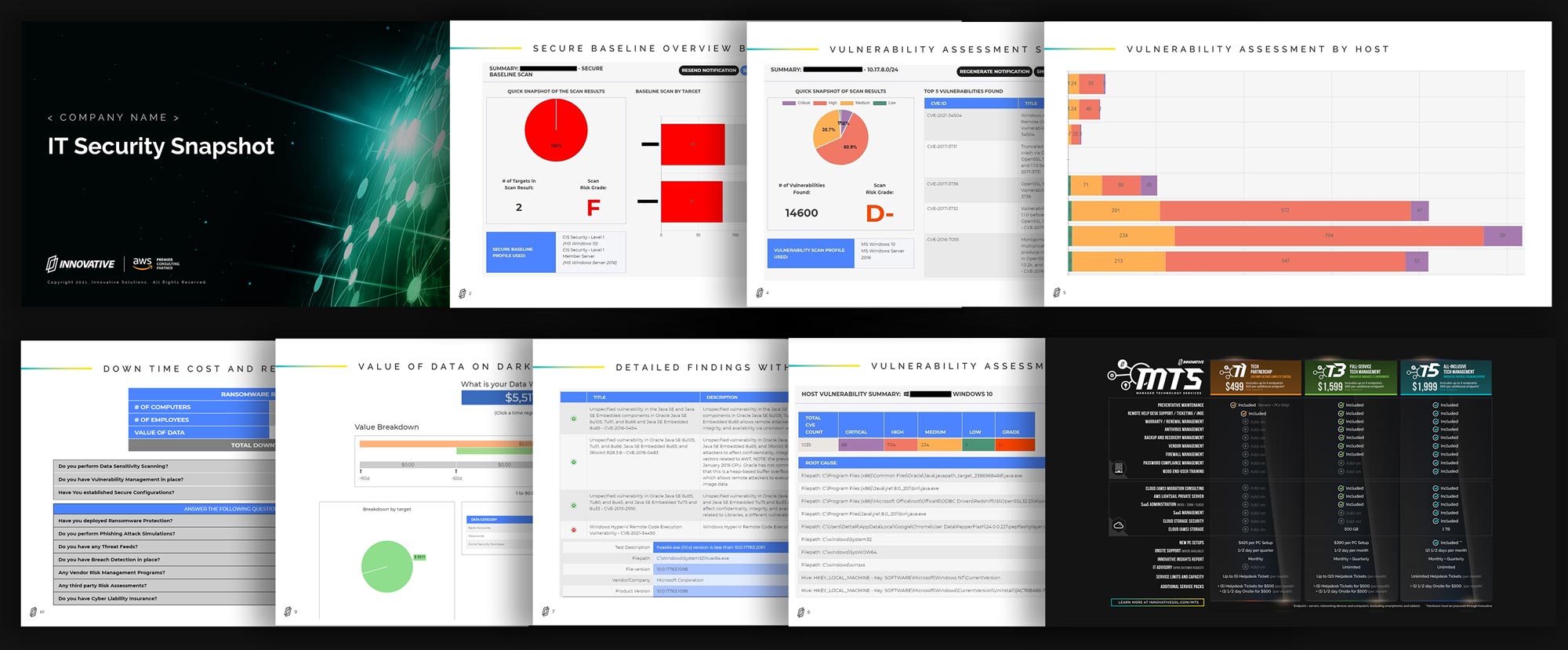
IT Security Snapshot is a great way to identify gaps and areas of increased risk as it relates to vulnerabilities and sensitive data within in your IT environment. We will deliver a published report of findings and a security scorecard, along with raw data exports of all scan results.
The goal is to help guide you towards achieving a greater security posture. It will help you identify areas of improvement as it relates to patch management, and understanding what sensitive data may be accessible within your environment, which increases your risk profile as a target for bad actors.
Do you know:
- Where your data is located?
- The classification of such data?
- Can there be multiple versions of the data?
- Who has access to this data?
- If access is open to anyone at any time?
- Do the devices hosting the data have vulnerabilities?
Can you create a mitigation plan to:
- Assign accountability to data owners
- Reduce the sensitive Data footprint
- Patch identified vulnerabilities on devices
- Securely configure devices
- Respond to host Integrity alerts
- Continuous awareness education
Your IT Security Snapshot report will include…
- A full security analysis and breakdown of your environment
- Security recommendations
- Identification of any security and compliance issues
- Any other issues with configuration
How it works
Step 1: Contact us to get started
Reach out to us to schedule a quick exploratory call or meeting
Step 2: Intro Call + Scoping
During this call, we review the scope of the environment in order to provide a quote and discuss any permissions needed to access your IT environment
Step 3: Setup + Analyze
Once a quote is signed, we move forward with set up to analyze your IT environment and prepare a curated report of all our findings
Step 4: Findings + Next Steps
During this call, our team will discuss your personalized IT Security Snapshot and discuss next steps in our partnership
